The expansion of NATO’s Cooperative Electronic Support Measure Operations protocol, better known as CESMO, continues with growing interest across allied nations.
One year ago, Armada reported that NATO’s Cooperative Electronic Support Measure Operations (CESMO) electronic intelligence processing protocol was being mooted to help enhance border security. The CESMO protocol was originally designed to help aircraft share hostile emitter location information so the latter can be avoided or engaged. The North Atlantic Treaty Organisation’s (NATO’s) SEWWG (Signals Intelligence and Electronic Warfare Working Group) is CESMO’s custodian.
How CESMO works
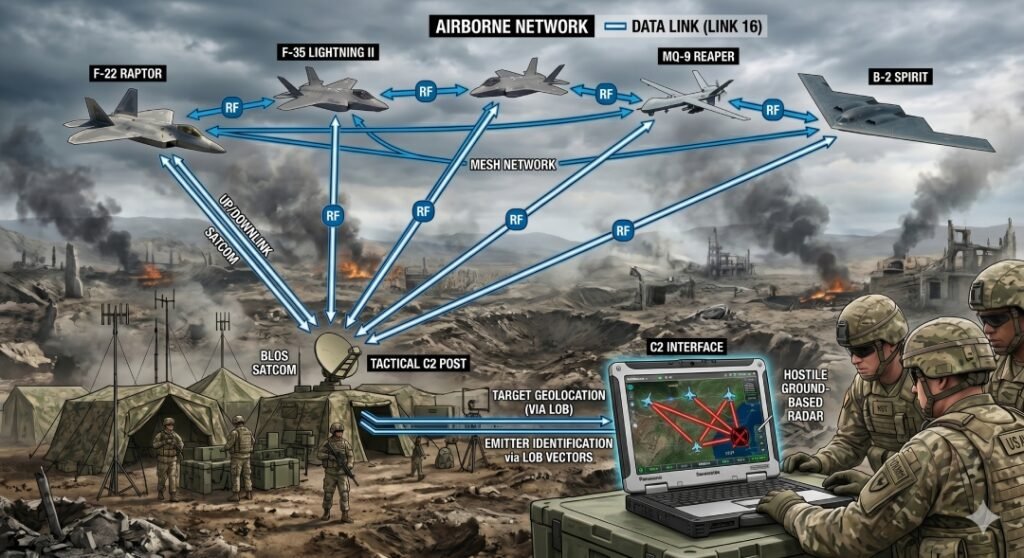
Military aircraft are routinely equipped with Radar Warning Receivers (RWRs) and Electronic Support Measures (ESMs). ESMs and RWRs protect aircraft by detecting, identifying and locating hostile ground-based air surveillance and fire control/ground-controlled interception radars. An RWR tends to give aircrew a relatively simple warning with details of a radar’s bearing relative to the aircraft. An ESM supplies more detailed information on the radar’s identity and location. The electronic support measure will also furnish specifics on the waveforms the radar is using although RWR and ESM functions can overlap.
RWRs and ESMs can use two mechanisms to detect and locate red force radars, chiefly Angle-Of-Arrival (AOA) and Time Difference of Arrival (TDOA). AOA determines the Line-of-Bearing (LOB) from one point to another, in this case between an aircraft and a hostile radar. Consider three aircraft flying in the vicinity of a ground-based air surveillance radar. One aircraft is flying towards the radar on a north-south bearing, the second is flying on an east-west radial away from it and the third is flying on a south-north bearing towards it. Each plane is equipped with an RWR which determines the radar’s line-of-bearing relative to the aircraft. All three planes detect the same radar transmission. The RWR on the first aircraft determines a southern LOB to the radar. The RWR on the second determines a westerly LOB while the third aircraft’s RWR determines a northerly line-of-bearing. By using this information, the radar’s position is determined as the point where all three bearings cross.
TDOA works slightly differently. We will stick with our three aircraft, all of which are flying the same courses in the vicinity of the hostile radar. One aircraft is 100 nautical miles/nm (185.2 kilometres/km) from the radar flying on north-south bearing. The second is 150nm (277.8km) from the radar flying away on an east-west radial. The third is 50nm (92.6km) away flying on a south-north bearing. Triangulation relies on the fact that radar transmissions travel at light speed (161,595 nautical miles-per-second/299,274 kilometres-per-second).
The same radar transmissions hit each aircraft’s RWR at different times. For the first plane it will take the transmissions 0.6 milliseconds to get there. For the second it will take 0.9 milliseconds and for the third 0.1 milliseconds. Calculating the time difference taken by the radar transmissions to arrive at each aircraft relative to their position computes the radar’s location. This data is fused with the aircraft’s position as derived from its navigation equipment and sent from each via their standard communications links. The data reaches a central computer housing the CESMO software. Once the data arrives, the software computes the point where the lines-of-bearing from each RWR meet.
The CESMO software ascertains the radar’s location retransmitting this to other friendly aircraft at risk of detection. The radar can then be avoided or engaged with kinetic, electronic and/or cyberattack. CESMO information is sent back out across the same communications links mentioned above. Data are carried across standard very/ultra-high frequency (30 megahertz to three gigahertz) links and tactical datalinks like NATO’s Link-16. Traffic is carried in IP (Internet Protocol) format messages absorbing under 16 kilobits-per-second of bandwidth. CESMO is a node-less network meaning there is no single point of network control. Should one platform sharing its information be lost this will not cause the CESMO network to collapse.
CESMO at the border
As our article last year noted, CESMO could help to enrich the overall intelligence picture of what is happening beyond a country’s frontiers. The protocol could be adapted to share details of signals-of-interest from aircraft radars, be they fire control radars, weather radars or radar altimeters. Alternatively, Signals-of-Interest (SOIs) from an aircraft’s radios could be exploited. Several antennas could be located on the ground close to the border on vantage points such as elevated terrain. Such sites provide a good field-of-view of the airspace over and beyond the border. SOIs could be captured by these antennas and then geolocated using AOA and TDOA processes.
CESMO’s capabilities would be ideal for detecting and tracking Uninhabited Aerial Vehicles (UAVs) flying close to the border via the radio links connecting the aircraft to its pilot. UAV flights close to the border may indicate that these aircraft are reconnoitring the frontier. The asset of CESMO is that it could provide the initial detection of a potential air target using the target’s radio and radar emissions. It may also be possible to identify this target via those emissions. CESMO target information could then be shared with national Integrated Air Defence Systems (IADSs) and accompanying ground-based air defences. Air defenders could take decisions on whether further investigations of a target are warranted, or even the target’s interception.
Protocol growth
The adoption of CESMO within and beyond NATO continues. According to Peter Ellis, technical fellow and principal engineer at Curtiss-Wright’s defence solutions business “(o)ver the past twelve months we have seen the implementation and development of the standard across multiple NATO member nations. We are also seeing interest from non-NATO countries as CESMO continues to mature and adoption becomes more prolific”. Curtiss-Wright provides hardware and software applicable to the CESMO protocol. Mr. Ellis continues that multinational exercises involving allied nations have been intrinsic to encouraging CESMO’s adoption: “During these exercises, participating countries get to experience first-hand the impact of EW data sharing and how easily CESMO can be integrated into their platforms”. The protocol has been used operationally since 2022. Beyond the discussion of CESMO to support the border security role, the protocol is being used to assist other missions like anti-submarine warfare, notes Mr. Ellis.
While CESMO brings a vital data sharing element to spectrum manoeuvre, and hence the capture and sustainment of electromagnetic superiority and supremacy, “effectors (still) need to be identified and employed to neutralise detected threats”, says Mr. Ellis: “Accordingly, there is a lot of focus now on how to coordinate both kinetic and non-kinetic effects through CESMO”. He adds that, at the policy level, a significant growth in SEWWG participation “is reflective of the growing amount of interest in and adoption of CESMO”.
by Dr. Thomas Withington