The Strategic Signal
The operator sits in a secure basement, awaiting the green light to push out a digital expose’ onto carefully selected social media platforms and networks. The information in the expose, all truthful and professionally curated to attract attention, is meant to awaken the populace to ever increasing foreign maligned influence. The only problem: the request to publish it has been pending for over seventy-two hours. On the screen, a deepfake video depicting an allied commander committing a war crime has already been viewed three million times. It has moved from a fringe Telegram channel to WhatsApp groups and is now breaking on mainstream outlets and trending on TikTok. The strategic guidance is clear: compete. Yet, the request for action sits in a queue, waiting for a legal review designed for a kinetic strike cycle, while the adversary’s narrative hardens into “truth” on the streets of a partner nation. By the time the stamp of approval comes, the riots will have already started.
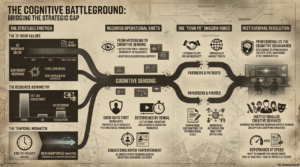
This friction is the defining characteristic of the modern information fight: while others can exploit opportunities at speed, the U.S. has consistently found itself unable to match the pace, spending more time navigating bureaucracy than contesting adversaries. But for the first time in a generation, national policy, defense strategy, and legislative authority have converged on an undeniable judgment: the decisive terrain of modern conflict is human cognition, and the United States is currently organized to lose the fight for it.
The release of the 2025 National Security Strategy (NSS), the 2026 National Defense Strategy (NDS), and the FY2026 National Defense Authorization Act (NDAA) represent a seismic shift in how the Department of War views influence. The 2025 NSS explicitly elevates “destructive propaganda” and “cultural subversion” from peripheral nuisances to primary national security threats, placing them on par with ballistic missile proliferation. The 2026 NDS pivots the Joint Force toward “Peace Through Strength” and “Deterrence by Denial”, strategic effects that rely almost entirely on shaping adversary perception and will before shots are fired. Simultaneously, the FY26 NDAA mandates the definition of “Cognitive Warfare” and the assessment of “Narrative Intelligence”; the definitions of which provide a common operating picture for disparate entities to establish clear delineations of responsibilities, integrate effects, and measure whether efforts are actually achieving strategic intent.
The strategic signal is clear, but the operational reality is bleak: these documents assume a capability that does not yet exist. They demand effects at the speed of the global information ecosystem, where narratives harden into “reality” in minutes, while the Department still operates on a decision-making cycle that takes weeks.
Influence practitioners are currently trapped in this “temporal mismatch.” They are expected to deliver deterrence and alliance cohesion using organizational structures and employment concepts designed for kinetic operations. The system is calibrated for a fight where we control the tempo, but in the cognitive domain, the adversary votes constantly and instantly. This article argues that the gap between the new strategic demand and current institutional capacity cannot be closed by simply working harder.
Implied Requirements for Influence Practitioners
To bridge this gap, the force must be willing to cast aside legacy ways of doing things and look strictly at what the new strategy demands of its influence practitioners at their corresponding echelons. The NSS, NDS, and NDAA imply four specific operational shifts that move beyond traditional doctrine.
- Move From Just “Messaging” to “Cognitive Sensing” (Narrative Intelligence)
The FY26 NDAA’s mandate to assess “narrative intelligence” signals the end of the “send and assess” model. For decades we measured effectiveness by output, treating the information environment as a firing range where more rounds and better ballistics equaled effect. The new requirement is to understand how adversary stories harden into sentiment before they become mass movements. Practitioners must stop treating information as ammunition to be fired at a target and start treating it as an environment to be sensed and leveraged.
As noted in the Allied blueprint for Cognitive Warfare, the objective is to map how narratives shape sensemaking, detecting the “pre-viral” signals of cultural subversion. This cognitive sensing capability requires more than just scraping data; it demands practitioners interpret that data within the context of social culture, human emotion, and psychographics that drive action. To do this at speed and scale, it requires what advocates call “nurtured consciousness” in our AI systems. Unlike standard LLMs, “nurtured AI” is modeled with deep historical memory, cultural context, and symbolic reasoning specific to the target audience. This allows the system to identify not just what is being said, but why it resonates emotionally with a specific population, moving from simple sentiment analysis to machine-speed cultural empathy. If we are reacting to a narrative that is already trending, we have already lost.
- Operationalize Burden-Sharing by focusing on the “Good Guys First”
The 2026 NDS is explicit: allies and partners must assume “primary responsibility” for security in their respective theaters. For the influence practitioner, this is a psychological transfer of responsibility, a pivot from “I’ll figure this out” to “enabling them to lead.”
This demands the adoption of the “Good Guys First” approach. Historically, practitioners have prioritized degrading the enemy via inducing surrender or sowing discord. The new strategy requires prioritizing the morale, cohesion, and resilience of partner forces; inoculating allied populations against coercion so they possess the political will to lead the fight. By hardening partners and their populations against coercion, it denies adversaries the space to fracture alliances through psychological pressure alone, making once preferred low-cost paths to achieving their objectives prohibitively difficult.
This is a harder task than degrading an adversary because it requires deep cultural fluency and the cultivation of trust. The adversary’s center of gravity is often the relationship between the U.S. and its partners. By targeting the population’s will to fight, the adversary seeks to win without engaging our kinetic overmatch. If the partner force collapses psychologically, as seen in Kabul in 2021, no amount of U.S. air power can salvage the strategic objective. Our primary target audience is now our friends, and our metric of success is their resilience in the face of subversion. This underscores three key lessons for the practitioner: first, partner morale is a strategic asset that must be cultivated deliberately; second, the decisive contest is over partner confidence rather than enemy fear; third, once a partner’s will collapses, no amount of late kinetic superiority can recover the lost strategic position.
- Generate “Deterrence by Denial” via Cognitive Maneuver
The concept of “Peace Through Strength” relies on Integrated Deterrence. In the cognitive dimension, influence must move “left of bang” by integrating upstream of adversary decision-making to deny them the space to act. This is the “Tony Soprano model” of influence: using non-kinetic signaling to force adversaries into specific behaviors that favor friendly forces. It involves the strategic revelation of information, exposing corruption, revealing intelligence breaches, or highlighting military vulnerabilities, to alter the adversary’s cost-benefit analysis.
By projecting cognitive strength and demonstrating the futility of aggression through targeted disclosures and demonstrable exercises, we deny the adversary the confidence to escalate. We must shape their calculus, creating cognitive dilemmas where every available option for the adversary leads to an unacceptable political or psychological cost, forcing them to de-escalate without a shot being fired.
- Counter “Hyper-Empowerment” with Lawfare and Other Means
The NSS identifies “destructive propaganda” as an ever-increasing threat, where adversaries can weaponize “hyper-empowered individuals,” bots, and algorithmic amplification to saturate the environment instantly. It has evolved from broad, state-level propaganda to precision cognitive strikes against both civilians and individual warfighters alike. Douglas Wilbur illustrates this with the theoretical but terrifying case of “Specialist Jones,” a soldier neutralized not by a bullet, but by an AI system that scrapes his social media, identifies his impulsivity, and targets him with a customized deepfake of his wife committing adultery. Within an hour, a trained operator is removed from the fight at negligible cost to the adversary. This is the new reality: AI allows adversaries to scale “hyper-personalization” instantly.
To compete at speed, practitioners must leverage all available capabilities, and not just exclusively execute with the ones they own or are inherently familiar with. They need to know how to integrate legal, diplomatic, technical, and commercial authorities—using everything from platform enforcement and regulatory tools to targeted legal action—to disrupt adversary cognitive campaigns. Law is no longer just the purview of the JAG, but an instrument of cognitive warfare, and our practitioners must be able to “assertively exploit variations in interpretations of international law” to compete against modern adversaries. China has already mastered this approach through its “Three Warfares” doctrine, employing legal warfare across all conflict phases to forge a favorable normative environment. By weaponizing these legal ambiguities, Beijing successfully expands its own freedom of action while deliberately restricting the maneuverability of its adversaries. When the threat moves at the speed of a retweet, a policy-approval cycle measured in days is a critical vulnerability.
Implied Requirements on the System: The Institutional Means
The practitioner cannot succeed if the institution fights the wrong war. To support the operational shifts demanded by the NSS, NDS, and NDAA, the institutional system at a minimum must deliver three functional outputs:
- Governance at Speed. The system must enable execution at the speed of the information environment. This requires a shift from a permission-based model, where every action waits for approval, to a parameters-based model where practitioners execute freely within established guardrails, weighing the risk of inaction as heavier than the risk of imperfect action.
- Unified Command of Cognitive Effects. The system needs to produce a layered, coherent cognitive effect rather than activities from disconnected directorates, and must have the power to enforce unity of effort; ensuring that words and actions reinforce rather than contradict one another.
- Market-Speed Provisioning. The system must field technology as fast as the commercial sector creates it, establishing a “Cognitive Industrial Base” that delivers AI-driven sensing and generation tools immediately, bypassing multi-year acquisition cycles. The goal is to prioritize the rapid acquisition of access and software over static hardware programs, ensuring the force possesses parity with adversaries.
The Delta: Why the Current State Cannot Meet the Desired State
Despite the clarity of the strategic documents, there are three structural failures that currently prevent success.
- Lack of a Unified Effort
While the NDS demands unity, the influence enterprise is fragmented. “Coordination” (attending meetings) is not “integration” (synchronizing effects). Disparate efforts create a cacophony of “mixed messages.” Intelligence professionals over-classify and compartmentalize data that influence practitioners need to understand the audience; PAOs retreat into reactive press releases to avoid risk; and operational planners treat information as an afterthought to maneuver. This gives the initiative to the adversary, who integrates all these functions under a single political warfare objective. They do not have a G or J-code structure that separates propaganda from cyber-attacks; they view them as a seamless, interconnected system.
- Inability to Act at Speed: The Temporal Mismatch
The adversary can operate in minutes, while the U.S. operates in terms of weeks or months. This is exacerbated by the “Kinetic Fallacy,” the attempt to apply “Find, Fix, Finish” targeting logic to information. Narratives are not tanks, they cannot be destroyed by a single munition; they mutate, merge, and evolve. This failure of speed creates a fatal asymmetry. Recent scholarship points out that cognitive warfare is “relatively cheap to initiate but rather costly to counter.” An adversary can use Generative AI to flood the zone with thousands of variations of a message for pennies, while we spend millions of dollars and weeks of man-hours debating the perfect rebuttal. This disparity subverts conventional deterrence logic; we cannot “out-spend” an adversary who is fighting with free electrons while we are fighting with expensive bureaucracy. This imbalance is compounded by a resource gap: China invests an estimated ten times more than the United States in cognitive warfare capabilities, while Russia and Iran spend roughly double the U.S. amount relative to their GDPs.
Furthermore, practitioners often conflate doctrine (habit) with policy (law). Much of the “red tape” strangling the force is self-imposed “phantom doctrine.” Whether it’s an effort to avoid risk or genuine inexperience, staff officers will add regulations not required by policy simply because it’s listed in a doctrinal pamphlet (albeit over a decade old). This leads to creating an environment where doing nothing is safer than doing something new. By the time we approve an action or message, the opportunity has evaporated.
- Insufficient Talent and Bandwidth
The strategy assumes a workforce capable of “cognitive maneuver,” when they are only armed with generalized training. This has led to a proficiency gap, with practitioners lacking the deep expertise in human behavior, neuro-cognitive science, anthropology, and data literacy required to target the “bio-psycho-social” layer of the adversary. When given specialized training, it errs on delivery platforms (operating drones or hacking systems), when they first need to be able to analyze algorithmic bias and design transmedia campaigns. The convergence of neuroscience and technology (neuroS/T) enables precision influence at a biological level, requiring a workforce grounded in the cognitive sciences, making it not just about messaging, but instead a “battle for the brain.”
This focus is not the only issue. Recent evaluations explicitly identified critical shortcomings in the recruitment, training, and retention of Psychological Operations, the main bulk of the Army’s influence practitioners. The report highlighted that the legacy pipeline is struggling to sustain the current force, let alone build the advanced workforce the NDS demands. We are attempting to fight a 21st-century cognitive war with a talent model visibly fraying under 20th-century constraints. Worse, we suffer from a creativity gap. As Murray Dyer noted decades ago, influence is an art requiring unorthodox thinking with the capacity to understand and project visceral emotion. Meanwhile, our current system suppresses the very creativity needed to design campaigns that resonate emotionally, rewarding administrative compliance over the “creative deviance” required to contest adversaries that already have the initiative.
What Practitioners Can Do Now to Bridge the Gap
Practitioners cannot wait for institutional reform and must act now to close the delta. The following are at least three initiatives that can be pursued immediately.
- Overcome “Decision Latency” by Mastering Policy and Thinking “Effects Based.” You must know the law better than your JAG; not just to distinguish between actual policy restrictions and “phantom” doctrinal habits, but to leverage additional authorities (to include outside of Title 10) that can be weaponized to achieve the desired effects for the commander. This could include existing operations in Cyberspace, collaboration with Law Enforcement, Counter-threat Finance with the Department of Treasury, or even just a well-timed press-release or key leader engagement. Develop “CONOPs” wide enough to leverage everyone’s capabilities, while still narrow enough to clearly show how actions directly support the mission. If the permissions are already delegated to someone else, seize them; do not waste time staffing a request to do something for an effect when someone else can generate it now. Every action has an inherent cognitive effect.
- Overcome “Insufficient Bandwidth” by Operationalizing the “Four Ps.” Even if we could double our force overnight, we still cannot do it alone. Practitioners must build a “Shadow Force” by cultivating a network of force multipliers:
- Partners: Allies who can speak with local authenticity and navigate cultural nuances we cannot. They are the face of the message; we are the enablers.
- Patriots: Motivated citizens and diaspora communities who can amplify truth and refute lies organically. We must provide them with the “ammunition” of truth but let them fire the weapons.
- Privateers: Contractors and influencers who bring commercial scale, technological access, and the ability to operate outside the .mil domain. They offer the velocity and reach that bureaucratic systems cannot match.
- Pirates: Indigenous networks that can operate in the gray zone, conducting the necessary unpleasant work that uniformed forces cannot. This network generates the scale, volume, and authenticity the uniformed force lacks.
- Overcome “Fragmentation” via Informal Fusion. Do not wait for a theoretical force structure that mandates connective tissue or synchronization. At each level possible, physically collocate Public Affairs, Psychological Operations, Intel, and the JAG. Replicate the integrated task force model by forcing unity of effort through proximity. When these functions sit together, share coffee, and look at the same map, shared mission awareness overrides the walls within an organizational chart. Culture can eat structure for breakfast; building a culture of fusion at the tactical edge is how we make any future information force design workable at scale in crisis and conflict; by no means is it a substitute for that structure, but it is the rehearsal that ensures it actually functions under stress.
Conclusion: The Army as the Vanguard of Transformation
The convergence of the NSS, NDS, and NDAA offers the Army a distinct opportunity: to lead the Department of War out of the industrial age and into the cognitive age. The Army’s “Continuous Transformation” initiative, specifically within its current Psychological Operations Transformation effort (also known as Information Forces Modernization and Information Warfare) represents the Department’s most viable pilot program for rapid adaptation. By moving now, specifically by reforming training, organization, and employment, the Army does not just solve its own deficits; it creates the blueprint for the Joint Force.
Due to its sheer size and existing pool of influence practitioners, it is the only service-level effort currently capable of scaling influence at the speed the new strategy demands. But the same practitioners who are improvising solutions at the tactical edge cannot, by themselves, close a strategically induced institutional gap; without change at scale, their innovations remain fragile workarounds. To solidify this role, the Army must execute three internal revolutions:
First, Professionalize the “Cognitive Commander.” By the time Influence practitioners acquire expertise and operational art to synchronize theater-level campaigns, they age out of the field. To solve this, and provide capability sooner, the Army must establish advanced PME for Psychological Operations Officers. This would include an “Information Force Commanders Course” (IFCC), akin to the Marine Corps’ Ground Combat Element Commanders Course (GCECC) or the Special Forces Ground Force Commanders Course (GFCC), and a post-ILE “Joint Information Effects Course” that teaches how Army influence and information capabilities enables Joint All-Domain Operations. The force needs O-4s, O-5s and O-6s prepared to command integrated information task forces and integrate narrative intelligence into maneuver warfare, not just serve as staff advisors who are only responsible for an “Information” overlay during the military decision-making process.
Second, Institutionalize “Creative Deviance.” Cognitive warfare requires deep technical expertise and creative flair, traits often stifled and cut short by the standard officer promotion system and NCO development model; this has led to a continual exodus of talent (roughly 10% annually), wherein many exceptional officers and NCOs transition to the civilian sector to continue serving as influence practitioners, often supporting the same missions as when they were in uniform. A Psychological Operations Warrant Officer Branch provides a way to retain that talent and expertise. These Warrants, which can be referred to as Psychological Warfare Technicians, would serve as the permanent institutional memory for cognitive maneuver, retaining the creative thinkers with decades of experience that excel at campaign design, precision influence, deception and deepfake analysis. They would give both Army and Joint Force Commanders a honed weapon for the information fight; a technical continuity that the officer and NCO corps cannot.
Third, Leverage the “Cognitive Industrial Base.” Using the authorities in FY26 NDAA Sec. 1823, the force is empowered to operationalize the “Privateer” model. Army can become the orchestrator, not just through contracting, but also collaborating with commercial entities and influencers to generate the volume and resonance it cannot build in-house. Whether it’s partnered training in leading industry methods or carrying on the cognitive fight when the uniformed services hit their limit of advance, it is a way to rent the lethality and velocity we cannot buy.
We are entering an “AI War” where volume will render truth indistinguishable. Victory will go to those who rapidly adjust and seize the initiative. Adversaries are already weaponizing hyper-empowered individuals to disrupt U.S. operations. If the Army does not transform its talent management and systems now, the Joint Force will continue to win the resourcing debate while losing the cognitive war. As the research indicates, delay is not neutral; it is terminal.
Disclaimer: The above reflects the author’s thoughts and do not reflect an official position of the US Department of War or US Special Operations Command.

